In a digitally networked world, a secure IT infrastructure is more important than ever. Companies that are classified as "critical infrastructures" (KRITIS) are considered to be particularly worthy of protection. If a KRITIS company fails, this can result in long-term supply bottlenecks and public safety can also be jeopardised.
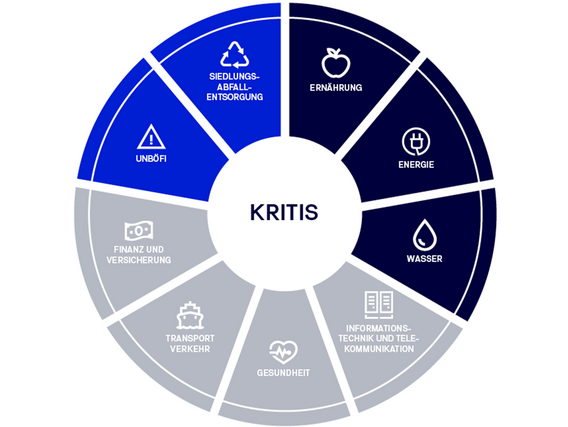
Until recently, seven different sectors in Germany belonged to the KRITIS. These include, for example, the energy, water, food, telecommunications, healthcare and finance sectors. As part of the IT Security Act 2.0 (IT-SIG 2.0), the sectors of municipal waste disposal and companies in the special public interest (UBI/UNBÖFI) have now also been added.
By lowering the thresholds in the KRITIS Regulation, the IT-SiG 2.0 now requires significantly more organisations to take effective measures to increase their IT security. In principle, the aim is to cover all companies that supply more than 500,000 people with their services and products.